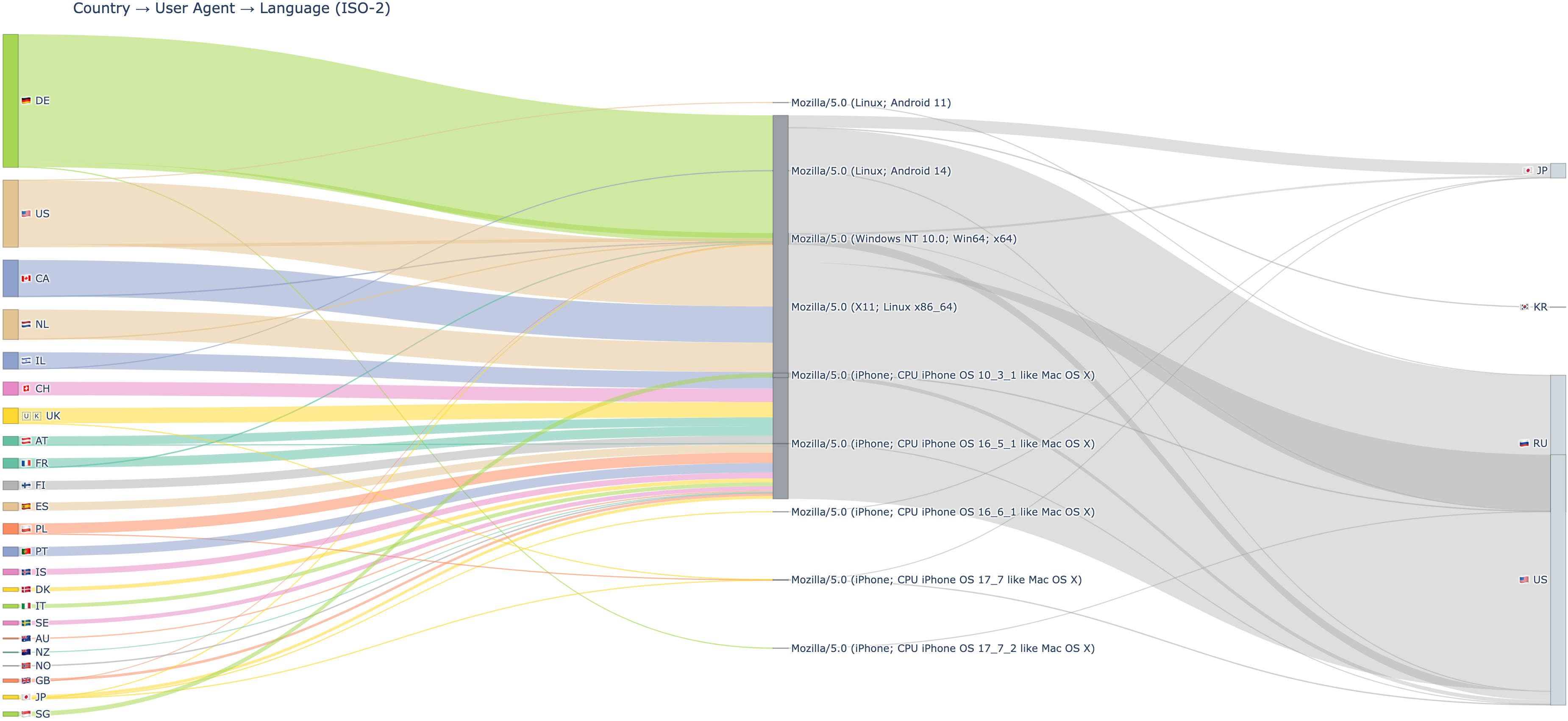
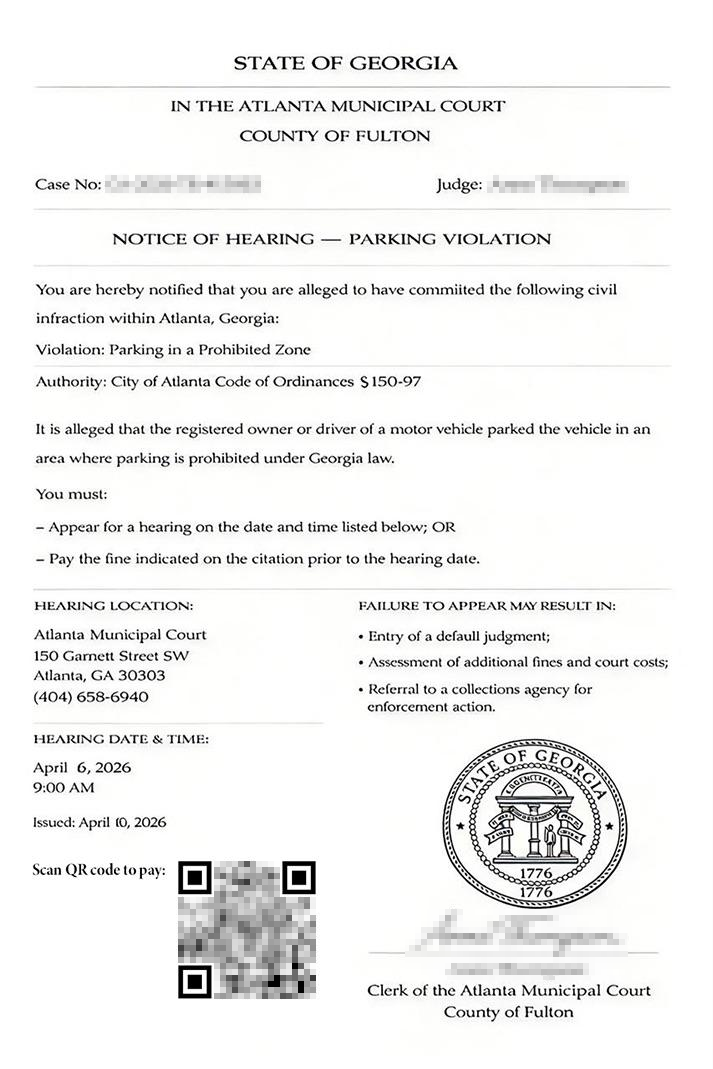
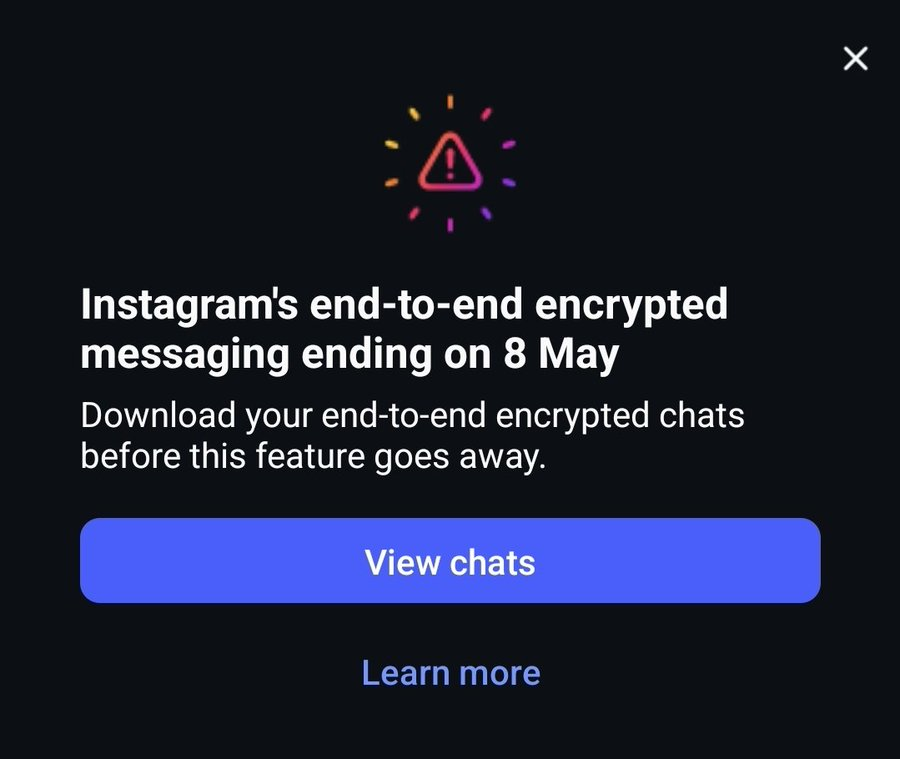
🔴 A threat isn't much of a threat if it can't reach the right victims. 📦 That's why many modern threat actors rely on cloakers and traffic distribution systems (TDS) to target, route, and hide at scale. In a six‑month joint effort analyzing four months of data with Confiant, we identified 15,500 domains configured to Keitaro instances and actively used in cyber campaigns. Keitaro is a legitimate ad tracker, but it is frequently misused by cybercriminals as an all‑in‑one tracker + TDS + cloaker in scam and malware campaigns. We encounter Keitaro in our investigations nearly every day, and we set out to quantify that abuse in the broader landscape. We're publishing a three‑part series to share what we learned. Part 1 focuses on a subset of actors who leverage AI in their operations, most of whom are tied to investment scams. At the end of the report, you'll find a link to our github repository that contains thousands of related Keitaro iocs.
#dns #threatintel #threatintelligence #cybercrime #cybersecurity #infosec #infoblox #infobloxthreatintel #scam #ai #keitaro #adtech #tds #trafficdistributionsystem #cloaker #cloaking #landscape #malvertising